Cybersecurity 101: Cybercrime - Dark Web - White Hat Hackers - Business Strategies
business resources|cybersecurity
20 Nov 2020

https://youtu.be/nFeMJuNjg2c
Global cybercrime costs will exceed $6 Trillion in the next years. From virtual bank heists to semi-open attacks from nation-states, the last couple of years has been rough on IT security, and has just been accelerated by the digitisation brought by the COVID-19 pandemic. To defend your business, multi-factor authentication and encryption are the biggest hacker obstacles.
suggest that there is a hacker attack every 39 seconds while 300,000 new malware is created every day. As of 2018, there were more than 800 million malware infections from 12.4 million back in 2009, being small and medium businesses one of the main targets for these attacks. In fact, the average cost of data for corporations breaches is $150+ million. The lack of preparation & cybersecurity strategy will have devastating effects on the integrity & survival of businesses & governments. Cyber-threats is a reflection of lack of preparation and a weakness in an organization's structure. Malware + web-based attacks continue to be the most expensive cybersecurity issues The cost of Ransomware (21%) and Malicious insider (15%) attacks types have been grown year after year. 92% of malware is delivered by email. Among all types of cybersecurity attacks, hackers have found that phishing attacks are the most successful. This has been accelerated by the COVID-19 outbreak. Since the pandemic started there has been
an uptick in sophisticated phishing email schemes by cybercriminals
. Malicious actors are posing as the Center for Disease Control and Prevention (CDC) or World Health Organization (WHO) representatives. These emails are designed to deceive and trick recipients into taking an action such as clicking a malicious link, or opening an attachment with a virus.
Other types of cybersecurity attacks include:
Man-in-the-middle attack
A MITM (man-in-the-middle) attack is where the attacker intercepts and relays messages between two parties who believe they are interacting with one another. It is also known as an eavesdropping attack. Once attackers are in the conversation, they can filter, manipulate, and steal sensitive information.
Distributed denial-of-service attack
Distributed denial-of-service (DDoS) attacks bombard an organization’s central server with simultaneous data requests. Multiple compromised systems are used to generate these data requests. A DDoS attack aims to stop the server from fulfilling legitimate requests, providing a situation for criminal hackers to extort the victim for money. The timeline of a DDoS attack can vary, with 15% of attacks lasting
.
SQL injection
SQL (Structured Query Language) is used in programming and is designed to manage data in relational database management systems. During SQL injections, criminal hackers insert malicious code into the server that uses SQL, which makes the server reveal sensitive information.
Zero-day exploit
When a network vulnerability is announced, there is a window of time before a patch or solution is used to fix it. Within that timeframe, cyber attackers will exploit the vulnerability.
The Deep And Dark Web
The dark web is a small subset of the deep web, which is part of the internet that is not found using search engines. That includes many websites that require users to log in with an username and password, and the deep web is estimated to be about 400 to 500 times larger than the common internet. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access.
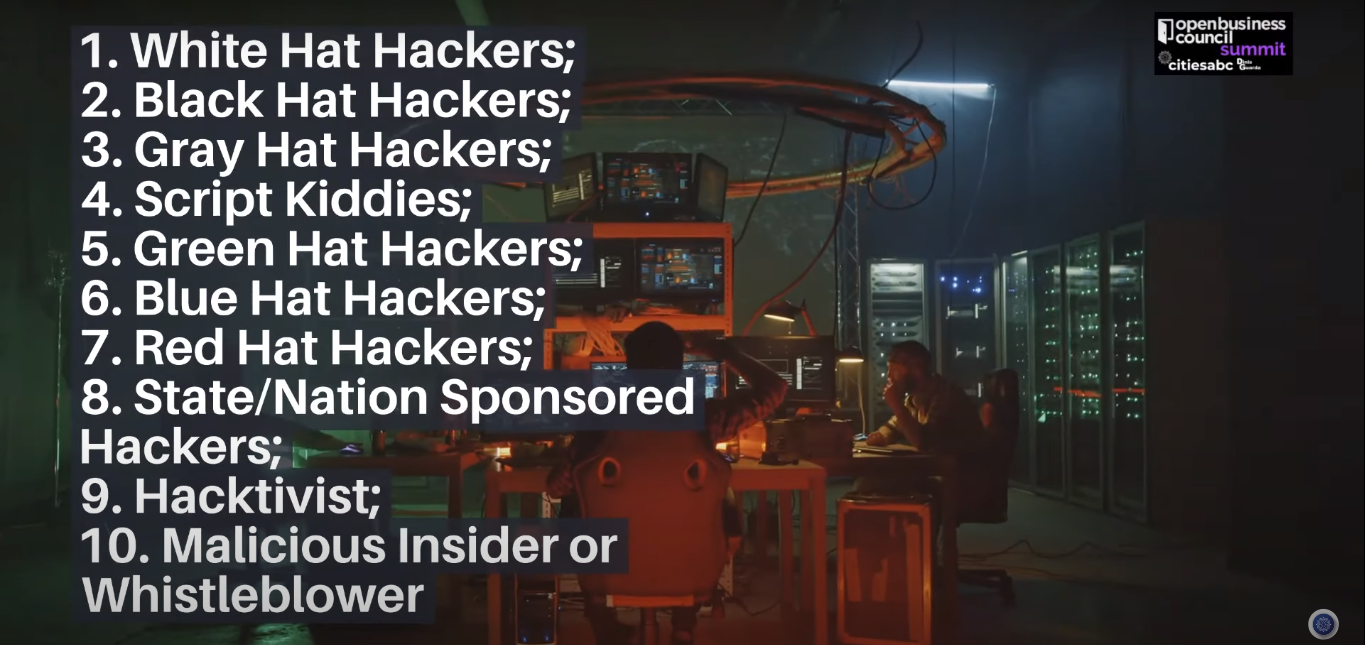
Type of Hackers
There are generally 10-types of Hackers: 1. White Hat Hackers; 2. Black Hat Hackers; 3. Gray Hat Hackers; 4. Script Kiddies 5. Green Hat Hackers 6. Blue Hat Hackers 7. Red Hat Hackers 8. State/Nation Sponsored Hackers 9. Hacktivist 10. Malicious Insider or Whistleblower. White Hat Hackers are the ones authorized or certified hackers who work for the government and organizations by performing penetration testing and identifying loopholes in their cybersecurity. There are over 715,000 cybersecurity experts employed in the US alone HackerOne for example represents a community of over 300,000 white hackers.
 Type of Hackers
Type of Hackers
Cybersecurity and Businesses
How Can You Identify Cybersecurity issues such as Malware Infections on Your business, organisation PC, Mac, or Mobile?
Information + Data Security is the fastest growing component of businesses' and organizations’ competitive strategy. The direct collection, management, and interpretation of business information, data, IP or the retention of day-to-day business intelligence processing is becoming the biggest asset for businesses and governments, and hackers know of their importance and value. An accurate vision of digital and behavioral gaps is crucial for a consistent business and organisation cyber-resilience. The basics have been around for a long time, but they still represent the first barrier against a cybersecurity breach: Antivirus and anti-malware.
“Passwords are like underwear: don’t let people see it, change it very often, and you shouldn’t share it with strangers.”
Chris Pirillo Likewise, common sense and IT literacy play a big role when setting up a cybersecurity defence. Obvious signs of malware infection is the increased presence of ads, banners, pop-ups, spam, alerts, and other unwanted communications. Any notable increase in these ads or pop ups is a clear indication that malware has infected your computer. You may even be alerted to the presence of malware with an announcement to that effect: Your System Has Been Hijacked. If security were all that mattered, computers and IT systems would never be turned on, let alone hooked into a network with literally millions of potential intruders
5 most efficient cyber defenders:
1. Preparation - Anticipation 2. Culture - Education 3. Detection - test 4. Reaction - action 5. Resilience - persistence
The cybersecurity market
is continuing its stratospheric growth and hurtling towards the trillion dollar mark:
“It takes 20 years to build a reputation and few minutes of cyber-incident to ruin it,”
said cybersecurity expert Stephane Nappo. Leaders need to nurture a cybersecurity culture message of influence because security is a culture and you need the business to take place and be part of that security culture.
How ready is your business for a cybersecurity hacking?







