business resources
Legacy System Modernization Process: A Step-by-Step Roadmap
17 Feb 2026

Modernizing a legacy system isn’t hard because the code is “old.” It’s hard because real businesses run on that code. Orders go through it. Invoices depend on it. Support teams live inside it. And the moment you touch it the wrong way, you don’t just ship a bug - you risk downtime, broken integrations, and angry stakeholders asking why “a technical project” is suddenly a business crisis.
This guide walks you through a practical legacy system modernization process you can use to modernize safely, in phases, with clear deliverables at every stage. It’s written for teams that want fewer surprises, a cleaner architecture, and measurable results - not a heroic rewrite that drags on for two years.
If you’re evaluating a partner or building your internal plan, you’ll see the same approach we use at CodeGeeks Solutions: modernize in controlled waves, protect critical flows, and prove value early - while keeping the lights on.
Legacy Software Modernization Process: What the “Process” Really Includes
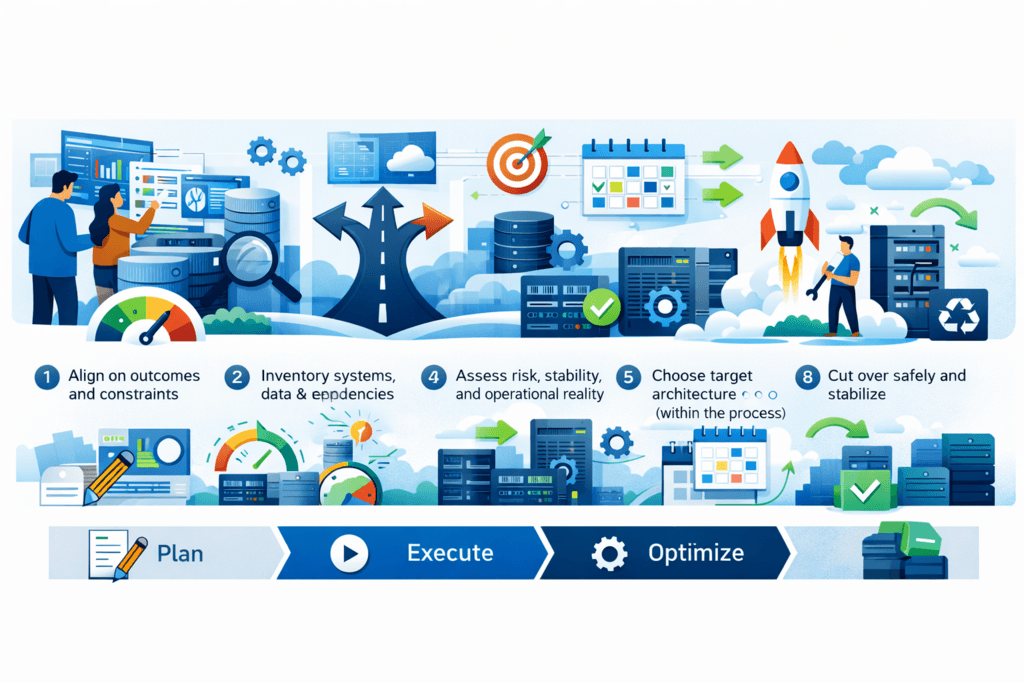
The legacy software modernization process is not one big migration weekend. It’s a sequence of decisions and checkpoints:
- Align on outcomes and constraints
- Inventory systems, data, and dependencies
- Assess risk, stability, and operational reality
- Choose the modernization path (within the process)
- Design target architecture + transition plan
- Plan execution and rollback
- Execute in waves with validation
- Cut over safely and stabilize
- Optimize and decommission what you no longer need
If your team skips steps (especially inventory, dependency mapping, and rollback planning), the project stops being “modernization” and turns into “incident management.”
Step 1: Build a Real Inventory (Apps, Data, Integrations, Owners)
Most modernization plans fail early because the team doesn’t actually know what they’re modernizing.
You need an inventory that answers simple but critical questions:
- What are the applications and modules? (including the “small” ones everyone forgot)
- Who owns each part? (decision-maker, tech owner, and business owner)
- Where does the data live? (DBs, files, third-party systems, spreadsheets that run payroll - yes, those exist)
- How does information move? (APIs, batch jobs, cron scripts, message queues, SFTP drops, ETL, manual exports)
- What environments exist? (dev/stage/prod, shadow environments, one-off “hotfix servers”)
- What are the contracts? (schemas, API expectations, file formats)
Deliverable you want after Step 1: a table you can hand to leadership that clearly shows the modernization surface area - and a dependency map your engineers trust.
What to watch for (the “silent killers”)
- Old batch jobs that run at night and nobody monitors
- File-based integrations that aren’t documented
- Reports built directly on production databases
- “Temporary” scripts that became permanent infrastructure
- Vendor systems that can’t be changed and will force your design
Step 2: Assess the Current State (Technical + Operational + Risk)
At this point you’re not writing a thesis. You’re building a reality check.
You want to know:
- Stability: where incidents come from, which parts are fragile, what fails under load
- Speed: what makes releases slow (manual steps, brittle tests, missing environments)
- Security: where risk is hiding (outdated libraries, auth gaps, weak secrets management)
- Maintainability: which areas are too coupled to change safely
- Cost: what’s expensive and why (licenses, infra, time spent firefighting)
A good assessment includes both code and operations. A system can be “clean” from an architecture perspective and still be a nightmare because deployments are manual and observability is weak.
Deliverables you want after Step 2:
- A scorecard (simple, consistent scoring across systems/modules)
- A risk register (what can break, how bad, how likely, and how you mitigate)
Fast assessment checklist (practical)
- Can you build and deploy without tribal knowledge?
- Do you have logs + metrics that explain failures, not just “it’s down”?
- Are critical flows covered by regression tests (even minimal ones)?
- Can you trace a customer request across services/modules?
- Are you running unsupported runtimes/databases?
- Do you have clear data ownership and schema change processes?
If the answer is “no” to most of those, your first modernization wave should include foundational work: CI/CD hygiene, observability, and risk controls - before major refactors.
Step 3: Choose the Modernization Path (Inside the Process)
This is where many teams accidentally derail the project. They treat “approach selection” like a philosophical debate instead of a decision inside a delivery plan.
You don’t need a perfect strategy. You need the right move for your constraints.
Here are the most common legacy system modernization approaches and when they tend to fit:
Rehost (“lift and shift”)
Good for: fast infra exit, data center deadlines, immediate cost structure changes
Risk: you keep your complexity; operational pain often follows you
Replatform
Good for: getting onto managed services, reducing ops burden, improving scalability
Risk: integration and data layers still need careful planning
Refactor
Good for: long-term maintainability, performance, security posture, developer speed
Risk: requires discipline and a phased plan to avoid breaking production
Rebuild
Good for: when the current system architecture blocks the business and incremental work can’t realistically get you there
Risk: high cost and time - risky without incremental delivery
Replace (buy/SaaS)
Good for: standard business processes where you don’t need heavy customization
Risk: hidden integration complexity and process change resistance
Retire / Retain
Good for: reducing scope and risk - often the smartest “modernization” is deleting what you don’t need
Risk: organizational buy-in (someone will fight to keep old systems)
Decision rule that works in real life:
If you can’t tolerate downtime and you need incremental value, favor phased modernization (often refactor + selective replatform) over big-bang rebuilds.
Step 4: Design the Target Architecture and the Transition Plan
This step is not “draw a pretty diagram.” It’s about preventing chaos later.
Your target architecture should answer:
- What are the domain boundaries? (what should be separate)
- Where is the source of truth for each data domain?
- How do services/modules communicate (API, events, async messaging)?
- How do you manage identity and permissions consistently?
- What does “done” look like (and what remains legacy)?
Your transition plan should show how you get there without pausing the business:
- What stays as-is initially
- What is wrapped, extracted, or replaced in waves
- How you keep old and new systems consistent during transition
Deliverables you want after Step 4:
- Target architecture (high-level and one level deeper for critical flows)
- Transition sequence (wave-by-wave plan tied to business value)
- Data strategy (migration waves + validation plan)
Data strategy (don’t postpone it)
Teams love refactoring code. Data is where projects get expensive.
Minimum you need:
- Migration approach (bulk + incremental, or continuous replication)
- Validation rules (reconciliation checks, totals, critical invariants)
- Rollback plan for data (not just code)
- Retention and audit requirements (especially in regulated industries)
Step 5: Plan Execution (Workstreams, Timeline, Rollback)
This is where “it sounded good” becomes “we can actually deliver this.”
Modernization is rarely one track. It’s multiple workstreams moving together:
- Application changes
- Data migration
- Infrastructure/platform changes
- Security hardening
- QA/test automation
- Operations (monitoring, alerting, on-call readiness)
This is also where you face the legacy modernization challenges most teams underestimate:
- hidden dependencies that surface late
- one critical flow that nobody can break (billing, auth, checkout, claims)
- business stakeholders wanting feature work at the same time
- teams overloaded by incidents while trying to modernize
Deliverables you want after Step 5:
- Wave plan with milestones (what ships when)
- “Definition of done” per wave (functional + operational)
- Rollback plan per release
- Risk controls: feature flags, canary releases, blue/green where possible
Risk controls that pay for themselves
- Feature flags for dangerous changes
- Canary releases for new components
- Shadow traffic / parallel runs for critical paths
- Hard “release gates” tied to monitoring signals, not opinions
Step 6: Execute in Waves (Build, Integrate, Validate)
Wave-based execution is what keeps modernization from becoming a never-ending program.
A wave should:
- Target a meaningful business slice (a workflow, a domain, a set of endpoints)
- Include integration and data implications
- End with measurable improvement (speed, stability, cost, maintainability)
What “good” looks like:
After each wave, you can point to something real: fewer incidents, faster releases, lower infra costs, reduced manual steps, improved performance.
Testing strategy for transitions
Don’t rely on “we tested it.” Build confidence systematically:
- Regression tests on critical flows
- Contract tests for integrations
- Data validation checks for every migration step
- Performance baselines (before/after)
- Security checks (dependency scanning, auth rules)
Step 7: Cutover Without Surprises (Release, Monitoring, Incident Plan)
Cutover is where leadership pays attention. It’s also where teams get blamed for things they didn’t plan for.
A safe cutover plan includes:
- Clear criteria for go/no-go
- Monitoring dashboards prepared in advance
- A hypercare window with ownership and escalation paths
- Runbooks that reflect the new system (not last year’s reality)
Operational readiness checklist:
- Alerts map to actions (not noise)
- On-call knows the new failure modes
- Logs and traces show root causes
- You can roll back quickly if needed
- You can replay or reconcile data if something drifts
Step 8: Stabilize, Optimize, and Decommission Legacy Components
This is the step teams skip - and then wonder why costs never go down.
Stabilization and optimization includes:
- Removing unused paths and services
- Eliminating duplicate infrastructure
- Decommissioning old licenses and servers
- Tightening security policies and secrets management
- Improving delivery pipelines now that the architecture is cleaner
What to measure after modernization
Use metrics that translate into business value:
- Lead time from change to production
- Deployment frequency
- Change failure rate
- MTTR (mean time to recovery)
- Cost-to-run per transaction/workflow
- Incident volume tied to legacy components (should trend down)
Legacy Application Modernization Process: Quick Checklist
If you want a one-page sanity check, here it is:
- Outcomes and constraints defined (uptime, compliance, deadlines)
- Inventory complete (apps, data, integrations, owners)
- Dependency map validated
- Current-state scorecard + risk register done
- Modernization path chosen per module/domain
- Target architecture + transition plan approved
- Data migration plan + validation rules created
- Execution waves planned with deliverables
- CI/CD, observability, and rollback strategy in place
- Cutover plan + hypercare + runbooks ready
- Decommission plan defined (to realize savings)
FAQ
How long does a legacy modernization process take?
It depends on scope, but the healthiest programs deliver first measurable wins in 6–12 weeks (foundation + one wave). Full modernization can be ongoing, but value shouldn’t be.
Can we modernize without downtime?
Often, yes - if you plan for phased delivery, invest in monitoring, and treat rollback as a first-class requirement.
Should we rebuild or refactor?
If you need incremental value and can’t stop the business, refactor/replatform in waves usually wins. Rebuild can work when the domain is well-defined and you can deliver in slices - not as one giant launch.
What usually breaks modernization projects?
Skipping inventory, underestimating data/integrations, weak rollback planning, and trying to do feature delivery + modernization without clear prioritization and capacity.
Share

Peyman Khosravani
Industry Expert & Contributor
Peyman Khosravani is a global blockchain and digital transformation expert with a passion for marketing, futuristic ideas, analytics insights, startup businesses, and effective communications. He has extensive experience in blockchain and DeFi projects and is committed to using technology to bring justice and fairness to society and promote freedom. Peyman has worked with international organisations to improve digital transformation strategies and data-gathering strategies that help identify customer touchpoints and sources of data that tell the story of what is happening. With his expertise in blockchain, digital transformation, marketing, analytics insights, startup businesses, and effective communications, Peyman is dedicated to helping businesses succeed in the digital age. He believes that technology can be used as a tool for positive change in the world.






